Official Public Political Attribution of Cyber Operations: State of Play and Policy Options
Study
When states become the target of malicious cyber activity, they have various options for responding politically. Which option states pursue depends primarily on whether they know who is behind a cyber operation. It is therefore essential to identify the perpetrator(s) of a cyber operation, a process also known as attribution. While states can engage in different forms of attribution, official public political attribution—a government entity’s public disclosure of information tying malicious cyber operations to another state through official channels—represents the most significant form from a cyber diplomacy standpoint.
In recent years, official public political attributions have gained traction as they allow states to highlight that they consider the attributed activity inappropriate, deter similar activities in the future, and raise awareness about threats. However, although more and more states are using official public political attributions, there is no clear shared understanding among states regarding how states should do so responsibly. In relation to international security, such common understandings can contribute to preventing misunderstandings and increasing the predictability of inter-state conduct.
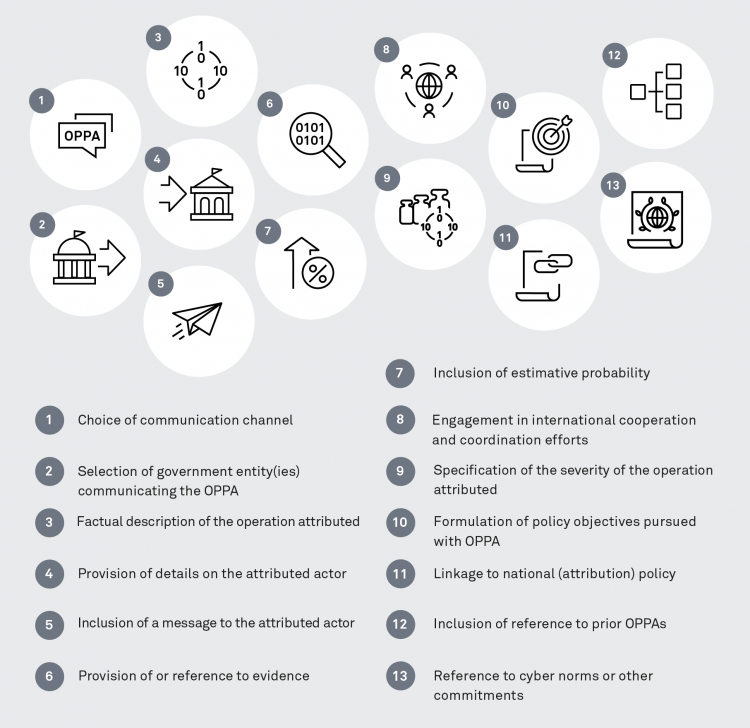
To stimulate an international strategic debate on this policy instrument that may eventually lead to a shared understanding, this analysis provides an overview of the current state of play and the policy options at a state’s disposal when engaging in official public political attributions of cyber operations. To do so, it focuses on the practices of four countries—Australia, Germany, Japan, and the U.S. Based on a comparison of 164 official public political attributions by the four selected states—109 by the U.S., 32 by Germany, 17 by Australia, and 6 by Japan—this paper proposes and applies an analytical framework of 13 parameters with corresponding options that serves to identify similarities and differences—areas of convergence and divergence—across countries.
In examining these cases, this analysis has found the following:
- Communication channels and designated government entities vary across countries and over time. The focus countries’ practices varied in that states used and prioritized different types of channels, including political, technical, criminal law channels and economic sanctions channels, to communicate their official public political attributions. The focus countries were similar in that especially their Ministries of Foreign Affairs and national cybersecurity, intelligence, or law enforcement agencies acted as communicators of the official public political attribution.
- Official public political attributions always provide details on the operations attributed. Many official public political attributions emphasized the targets or victims of the operations, followed by information on when the operations took place. At times, states also mentioned the damage and harm caused by the operations attributed.
- Official public political attributions differ in how they specify the attributed actor and sometimes include a message addressed to the actor. The focus countries published attributions with varying levels of specificity, ranging from attributions mentioning individuals working for entities of a particular state to attributions with exclusive references to Advanced Persistent Threat groups, with a tendency toward increased specificity in recent years. States sometimes included appeals to the attributed actor to cease the operation attributed and expressed that they reserved the right to initiate further consequences.
- Only some official public political attributions mention evidentiary information and estimative probability. The focus countries occasionally mentioned technical evidence and cited governmental and non-governmental sources in their attribution decisions, with a slight increase in the amount of mentions and citations over time. States sometimes provided specific technical information to support their political attributions. In a few instances, states included levels of confidence or likelihood to quantify the certainty of their attribution assessments.
- States increasingly coordinate their official public political attributions with like-minded countries. The focus countries coordinated their official public political attributions internationally in three main ways: participating in internationally coordinated attributions, supporting public attributions of another state with or without their own attribution assessment, and retrospectively endorsing the official public political attribution of another state. In recent years, the focus countries predominantly used the first way through joint statements or advisories, either through ad hoc, like-minded constellations or institutionalized processes within the EU.
- States regularly explain why they attribute, pointing to the operation, their policies, and/or international commitments. The focus countries often provided reasoning for why they attributed a particular cyber operation, especially when using political channels, by outlining the severity of the operation, formulating policy objectives, linking the attribution to general policy, referencing prior official public political attributions, or alluding to international commitments.
Given the varied ways in which states carried out their official public political attributions, the degree and scope of international convergence regarding how to conduct official public political attribution is liited among the four states at present.
For official public political attribution to mature as a policy instrument, a nuanced international policy debate is required, and decision-makers should seek ways to increase convergence, despite, or precisely because of, the topic’s sensitivity. Since many states are currently either systematizing or establishing their policies and processes on (public) attribution, there is a political momentum for inter-state exchanges to build and operationalize shared understandings.
Christina Rupp & Dr. Alexandra Paulus